Mastering the process of detecting hacking attacks and properly extracting evidence to report the crime and conduct audits.
Next DATES 17-Jun-2024, Register now 14-Oct-2024, Register now
course evaluation 4.8 in 5
Introduction
This course is available to be delivered in a classroom and Live-Training model.
Live Training brings you the dynamic environment of the classroom, to your desk. Using your computer, you interact with the trainer and the trainees as if you were with them in the classroom.
Click to learn how >
Live Online Training works <
CHFI is a comprehensive course covering major forensic investigation scenarios that enables students to acquire necessary hands-on experience regarding various forensic investigation techniques. Learn how to utilize standard forensic tools to successfully carryout a computer forensic investigation which can better prepare you to aid in the prosecution of perpetrators.
Battles between corporations, governments, and countries are no longer fought using physical force. Cyber war has begun and the consequences can be seen in every day life. With the onset of sophisticated cyber-attacks, the need for advanced cyber security and investigation training is a mandate in the present day. If you or your organization requires the knowledge or skills to identify, track, and prosecute the cybercriminals, then this is the course for you. This course helps students to excel in digital evidence acquisition, handling and analysis in a forensically sound manner. Acceptable in a court of law, these skills will lead to successful prosecutions in various types of security incidents such as data breaches, corporate espionage, insider threats and other intricate cases involving computer systems.
Training Methodology
EC-Council releases the most advanced Computer Forensic Investigation program in the world. CHFIv8 presents a detailed methodological approach to computer forensics and evidence analysis. It is a comprehensive course covering major forensic investigation scenarios that enable students to acquire hands-on experience on various forensic investigation techniques and standard tools necessary to successfully carry-out a computer forensic investigation.
Audience
The CHFI program is designed for all IT professionals involved with information system security, computer forensics, and incident response.
Prerequisites
It is strongly recommended that you attend the CEH class before enrolling into CHFI program.
Your own laptop is required - bring your laptop to training.
Duration (days)
5 days
Learning Objectives
At the end of the course students should be able to:
- The computer forensic investigation process and the various legal issues involved
- Evidence searching, seizing and acquisition methodologies in a legal and forensically sound manner
- Different types of digital evidence, rules of evidence, digital evidence examination process, and electronic crime and digital evidence consideration by
crime category
- Roles of first responder, first responder toolkit, securing and evaluating electronic crime scene, conducting preliminary interviews, documenting electronic crime scene, collecting and preserving electronic evidence, packaging and transporting electronic evidence, and reporting the crime scene
- How to set up a computer forensics lab and the tools involved in it
- Various file systems and how to boot a disk
- Gathering volatile and non-volatile information from Windows
- Data acquisition and duplication rules, validation methods and tools required
- How to recover deleted files and deleted partitions in Windows, Mac OS X, and Linux
- The process involved in forensic investigation using AccessData FTK and EnCase
- Steganography and its techniques, Steganalysis, and image file forensics
- Password Cracking Concepts, tools, types of password attacks and how to investigate password protected files
- Different types of log capturing, log management, time synchronization, and log capturing tools
- How to investigate logs, network traffic, wireless attacks, and web attacks
- How to track e-mails and investigate e-mail crimes
- Mobile forensics and mobile forensics software and hardware tools
- How to write investigative reports
Program
- Computer Forensics in Today's World
- Forensics Science
- Computer Forensics
- Forensics Readiness
- Cyber Crime
- Cyber Crime Investigation
- Corporate Investigations
Reporting a Cyber Crime
- Computer Forensics Investigation Process
- Investigating Computer Crime
- Steps to Prepare for a Computer Forensics Investigation
- Computer Forensics Investigation Methodology
- Searching and Seizing Computers
- Searching and Seizing Computers without a Warrant
- Searching and Seizing Computers with a Warrant
- The Electronic Communications Privacy Act
- Electronic Surveillance in Communications Networks
- Evidence
- Digital Evidence
- Digital Data
- Types of Digital Data
- Rules of Evidence
- Electronic Devices: Types and Collecting Potential Evidence
- Digital Evidence Examination Process
- Electronic Crime and Digital Evidence Consideration by Crime Category
- First Responder Procedures
- Electronic Evidence
- First Responder
- Roles of First Responder
- Electronic Devices: Types and Collecting Potential Evidence
- First Responder Toolkit
- First Response Basics
- Securing and Evaluating Electronic Crime Scene
- Conducting Preliminary Interviews
- Documenting Electronic Crime Scene
- Collecting and Preserving Electronic Evidence
- Packaging and Transporting Electronic Evidence
- Reporting the Crime Scene
- Note Taking Checklist
- First Responder Common Mistakes
- Computer Forensics Lab
- Setting a Computer Forensics Lab
- Investigative Services in Computer Forensics
- Computer Forensics Hardware
- Computer Forensics Software
- Understanding Hard Disks and File Systems
- Hard Disk Drive Overview
- Disk Partitions and Boot Process
- Understanding File Systems
- RAID Storage System
- File System Analysis Using The Sleuth Kit (TSK)
- Windows Forensics
- Collecting Volatile Information
- Collecting Non-volatile Information
- Windows Memory Analysis
- Windows Registry Analysis
- Cache, Cookie, and History Analysis
- MD5 Calculation
- Windows File Analysis
- Metadata Investigation
- Text Based Logs
- Other Audit Events
- Forensic Analysis of Event Logs
- Windows Password Issues
- Forensic Tools
- Data Acquisition and Duplication
- Data Acquisition and Duplication Concepts
- Data Acquisition Types
- Disk Acquisition Tool Requirements
- Validation Methods
- RAID Data Acquisition
- Acquisition Best Practices
- Data Acquisition Software Tools
- Data Acquisition Hardware Tools
- Recovering Deleted Files and Deleted Partitions
- Recovering the Deleted Files
- File Recovery Tools for Windows
- File Recovery Tools for MAC
- File Recovery Tools for Linux
- Recovering the Deleted Partitions
- Partition Recovery Tools
- Forensics Investigation using Access Data FTK
- Overview and Installation of FTK
- FTK Case Manager User Interface
- FTK Examiner User Interface
- Starting with FTK
- FTK Interface Tabs
- Adding and Processing Static, Live, and Remote Evidence
- Using and Managing Filters
- Using Index Search and Live Search
- Decrypting EFS and other Encrypted Files
- Working with Reports
- Forensics Investigation Using EnCase
- Overview of EnCase Forensic
- Installing EnCase Forensic
- EnCase Interface
- Case Management
- Working with Evidence
- Source Processor
- Analyzing and Searching Files
- Viewing File Content
- Bookmarking Items
- Reporting
- Steganography and Image File Forensics
- Steganography
- Steganography Techniques
- Steganalysis
- Image Files
- Data Compression
- Locating and Recovering Image Files
- Image File Forensics Tools
- Application Password Crackers
- Password Cracking Concepts
- Types of Password Attacks
- Classification of Cracking Software
- Systems Software vs. Applications Software
- System Software Password Cracking
- Application Software Password Cracking
- Password Cracking Tools
- Log Capturing and Event Correlation
- Computer Security Logs
- Logs and Legal Issues
- Log Management
- Centralized Logging and Syslogs
- Time Synchronization
- Event Correlation
- Log Capturing and Analysis Tools
- Network Forensics, Investigating Logs and Investigating Network Traffic
- Network Forensics
- Network Attacks
- Log Injection Attacks
- Investigating and Analyzing Logs
- Investigating Network Traffic
- Traffic Capturing and Analysis Tools
- Documenting the Evidence Gathered on a Network
- Investigating Wireless Attacks
- Wireless Technologies
- Wireless Attacks
- Investigating Wireless Attacks
- Features of a Good Wireless Forensics Tool
- Wireless Forensics Tools
- Traffic Capturing and Analysis Tools
- Investigating Web Attacks
- Introduction to Web Applications and Webservers
- Web Logs
- Web Attacks
- Web Attack Investigation
- Web Attack Detection Tools
- Tools for Locating IP Address
- Tracking Emails and Investigating Email Crimes
- Email System Basics
- Email Crimes
- Email Headers
- Steps to Investigate
- Email Forensics Tools
- Laws and Acts against Email Crimes
- Mobile Forensics
- Mobile Phone
- Mobile Operating Systems
- Mobile Forensics
- Mobile Forensic Process
- Mobile Forensics Software Tools
- Mobile Forensics Hardware Tools
- Investigative Reports
- Computer Forensics Report
- Computer Forensics Report Template
- Investigative Report Writing
- Sample Forensics Report
- Report Writing Using Tools
- Becoming an Expert Witness
- Expert Witness
- Types of Expert Witnesses
- Scope of Expert Witness Testimony
- Evidence Processing
- Rules for Expert Witness
- General Ethics While Testifying
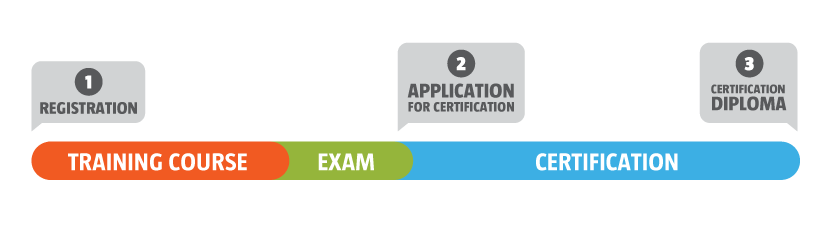
Exam
The CHFI 312-49 - Computer Hacking Forensic Investigator (CHFI) - EC-Council exam will be conducted on the last day of training
Number of Questions: 150
Passing Score: 70%
Test Duration: 4 hours
Test Format: Multiple choice
Certification
CHFI Program certifies individuals in the specific security discipline of computer forensics from a vendor-neutral perspective. The C|HFI certification will fortify the application knowledge of law enforcement personnel, system administrators, security officers, defense and military personal, legal professionals, bankers, security professionals, and anyone who is concerned about the integrity of the network infrastructure.
The CHFI 312-49 exam will be conducted on the last day of training.
Trainer
Trainer certified by EC-COUNCIL.
General Information
CLASSROOM TRAINING
- Training in English language.
- Online training material in English, with online access for 1 year. If you wish, you can purchase the manual in paper format. Please let us know in the registration form. Fees apply.
- Hands on Labs - environment that simulates a real time information infrastructure. The iLabs is a subscription based service that allows students to log on to a virtualized remote machine running Windows 2008 Server to perform various exercises featured in the CHFI Lab Guide. All you need is a web browser to connect and start experimenting. The virtual machine setup reduces the time and effort spent by instructors and partners prior to the classroom engagement. It is a hassle free service available 24/7 x number of days subscribed.
- Behaviour Participation Certificate with 40 CPD/CPE credits.
- EC-COUNCIL Certificate.
- EC-COUNCIL Exam. You can schedule the exam within 11 months after training. The exam is available online or computer-based at Behaviour facilities
- Coffee break in the morning and afternoon (Applies to all training that take place in Behaviour facilities)
LIVE ONLINE TRAINING
- Training in English language.
- Online training material in English, with online access for 1 year.
- Hands on Labs - environment that simulates a real time information infrastructure. The iLabs is a subscription based service that allows students to log on to a virtualized remote machine running Windows 2008 Server to perform various exercises featured in the CHFI Lab Guide. All you need is a web browser to connect and start experimenting. The virtual machine setup reduces the time and effort spent by instructors and partners prior to the classroom engagement. It is a hassle free service available 24/7 x number of days subscribed.
- Digital Behaviour Participation Certificate with 40 CPD/CPE credits.
- EC-COUNCIL Certificate.
- EC-COUNCIL Exam. You can schedule the exam within 11 months after training. The exam is available online.
Dates and Price
Click on “Price and Registration” to access more information and also the price:
Guaranteed Dates Program
(*) All dates of this course are guaranteed only for the events that take place in Lisbon. In other locations the events are subject to a minimum number of participants. On Behaviour all courses at Lisbon occur regardless of the number of trainees in room. The concept of setting up classes does not exist in our educational model, which is why all public dates, presented on the website, are guaranteed. So if you're in Portugal or anywhere else in the world, you can prepare your week and your trip, as long as you ensure your registration in the course.
Volume Discounts
For companies, Behaviour offer discounts, starting from the registration of the 2nd participant, in the same course and on the same date. Simulate the prices for the number of participants you want to
training@behaviour-group.com or contact us via chat.
Hotels and Useful Information
Know where you can stay in Lisbon, near Behaviour.
For more information please see >> Booking <<